Interfacing the law research Zalan Szakacs: Difference between revisions
No edit summary |
No edit summary |
||
| Line 13: | Line 13: | ||
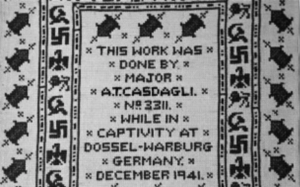
[[File:Screen Shot 2018-04-30 at 16.49.48.png|thumb| Historical case #1 During WWII, a Nazi captive cross-stitches a seemingly innocently looking decorative pattern around the border. The Nazi's never found out that it was Morse code spelling out: "God Save the King" and "Fuck Hitler".]] | [[File:Screen Shot 2018-04-30 at 16.49.48.png|thumb| Historical case #1 During WWII, a Nazi captive cross-stitches a seemingly innocently looking decorative pattern around the border. The Nazi's never found out that it was Morse code spelling out: "God Save the King" and "Fuck Hitler".]] | ||
[[File: | [[File:Amy Suo Wu-906b124d.jpg|thumb|Amy Suo Wu, A Media Archeology of Steganography, 2015] | ||
Revision as of 16:00, 30 April 2018
[[File:Amy Suo Wu-906b124d.jpg|thumb|Amy Suo Wu, A Media Archeology of Steganography, 2015]
Research ideas
Research questions:
- How would be possible to set up a pirate library through steganography?
- Which technologies would be used?
- Where would be the books hidden? JPG, PDF, MP3, WAV, EXIF?
- Which books would be included?
- How do you link them?
- Which interface to use?
- Which cataloging system to use?
- How could layering (text, images, metadata) become the navigation element?
- How could be pirated & steganographed books brought back to the "official" library?
- How could the reader find those books in the library?
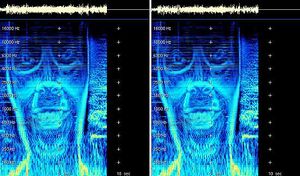
- How would it be possible to translate the texts into audio and while playing the audio the images would appear in frequency levels?
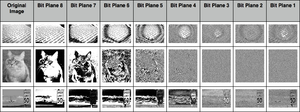
For my research I want to look into using several steganography tools through python to explore abusing file formats, such as hiding books in other books, texts in images, images in audio, etc. These experiments would create the foundation for programming the steganographed pirate library.
Research thought:
interest in hiding files in other files (imagine a PDF with an audio file?) A sound file has a whole library inside it. JPEG has free space inside it. (metadata ... EXIF data .... ) Steganography
hiding books in other books
censorship
books on the blacklist
read&seek
pirate library is pirating it’s own files
hiding pirated books in “official” library
Research references
→ Funky File Formats
Binary tricks to evade identification, detection, to exploit encryption and hash collisions.
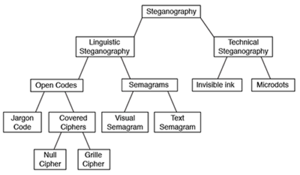
→ Steganography
Digital steganography, a set of algorithmic techniques for hiding data in files, is often used to hide text messages (or other digital content) within the bits of an image. In contrast to cryptography, steganography allows to hide the very fact that you are trying to hide something, an aspect that makes it really desirable for hidden communications or classified information leakage.
→ Javier Lloret - On opacity (2016)
→ Hiding in Plain Sight. Amy Suo Wu's The Kandinsky Collective
→ Introduction to Steganography
→ Using PIL → Hack This: Extract Image Metadata Using Python
→ ExifRead 2.1.2 Exif
Bibliography
Articles are saved in this Zotero library.