User:Michaela/thesis: Difference between revisions
| Line 9: | Line 9: | ||
==QUESTIONS I WANT TO ADDRESS IN MY ESSAY== | ==QUESTIONS I WANT TO ADDRESS IN MY ESSAY== | ||
'''#problem_aspect # | '''#problem_aspect #3'''<br> | ||
THEME: PRIVACY IN DIGITAL REALM <br> | |||
THEME: OWNERSHIP/ DIGITAL PROPERTY/ PROPERTY RIGHTS <br> | |||
'''#problem_aspect #2'''<br> | |||
SUB_THEME: PRIVACY IN DIGITAL REALM <br> | |||
The ethical issue I want to address is: who has the right to withdrawal someone's data and how this data could be used, reused or misused?<br> | The ethical issue I want to address is: who has the right to withdrawal someone's data and how this data could be used, reused or misused?<br> | ||
'''#problem_aspect # | '''#problem_aspect #3'''<br> | ||
SUB_THEME: AUTHORSHIP/CO-AUTHORSHIP/ MULTIPLE - AUTHORS<BR> | |||
The problematic aspect of the recovered data: who is the actual author of the final work?<br> | The problematic aspect of the recovered data: who is the actual author of the final work? Is it me or the <br> | ||
==INTRO== | ==INTRO== | ||
Revision as of 15:26, 3 February 2014
Useful links:
A Guide to Essay Writing
Draft_ thesis plan:
ABSTRACT
QUESTIONS I WANT TO ADDRESS IN MY ESSAY
#problem_aspect #3
THEME: OWNERSHIP/ DIGITAL PROPERTY/ PROPERTY RIGHTS
#problem_aspect #2
SUB_THEME: PRIVACY IN DIGITAL REALM
The ethical issue I want to address is: who has the right to withdrawal someone's data and how this data could be used, reused or misused?
#problem_aspect #3
SUB_THEME: AUTHORSHIP/CO-AUTHORSHIP/ MULTIPLE - AUTHORS
The problematic aspect of the recovered data: who is the actual author of the final work? Is it me or the
INTRO
How do we leave a trace of an online presence? The amount of traces/ digital traces in form of caches, cookies, footprint of the browser is stored, tracked and dumped in the system. Various tools – PGP (encrypting your email), browser plug- ins, private networks (VPN) – are used to prevent our location to be tracked, our data to be exposed. All of which limits the traces we leave but it doesn't completely erase them. Driven by my personal motivation to explore the limitations of technology and different methods of resistance I became sceptic about the possibility of being able to not leave traces or in other words the (im)possibility to erase the digital footprint. The common methods to erase files from systems do not delete them permanently. Those files remain hidden, abandoned in hard drives. The traces left remain present within time in the medium, allowing to be retrieved and becoming a subject of study.
THECHNICAL ASPECT
The discovered cluster must be treated as an ideal representation of data that could be used as a way of recovering the original data back from the “ideal” format. This is the idea of data recovery approach: not only to use the data for finding clusters but also to use the clusters for recovering data. In a general situation, the data recovered from the sumarized custers can not fit the original data exactly, which can be due to various factors such as present of noise in the data.
Data Entry: research on how to completely erase your data from the operating system. rmv command does not delete the file permanently" or non-restorative. I found indulging the fact that there is a command line "shred" ( available only on linux ), poorly used because of its damaging consequences. Shred erases all the information, by overwriting 20 times or so. There is no "shred" command in OS x instead there is a replacement or security remove command called srm. In comparison with Mac OS x, based on Unix system, a file could be overwritten only three times at the time. In relationship to that I find interesting approach of how to defeat the privace issue by information overflow or noising the channel, by overwriting something infinitive times instead of trying to denoise it.
'data erasure' term - or the only way to erase data permanently is physically to destroy a hard disk drive. In the past shredders were used to destroy confidential, secret papers now there are replaces by data shredders.
Questions about e-waste and digital recycling, digital trash and data recycling. Except the physical implementation of data storage of digital trash camps outrageously sent to remote areas in Africa nevertheless there is the ethical issue or who has the right to intervene with someone's data.
PROJECT
DESCRIPTION
I have started a process of retrieving old hard drives disks (data storage) restoring the data out of them, in order to examine abandoned data and leftover traces. By doing this I am exploring the problematic aspect of data erasure. The hard drive, in this case a rather obsolete object, serves as an ultimate storage of data, container of past and present, which could be also invaded and investigated further. The traces of information are exponential they contain various sources...they travel, scattered being trade -transacted or serve as a found footage for artistic intervention. This project is trigger by the idea of how the data trace is permanent, could not be destroyed or erased completely. It has been encapsulated within the time, the code and the medium itself.
METHODOLOGY
I am working on a series of projects related to the topic of these found traces, which will end up leading to the final graduation project. I would like to incorporate a poetic aspect of the retrieve data and the idea of the erasure as the main motive in the final work.
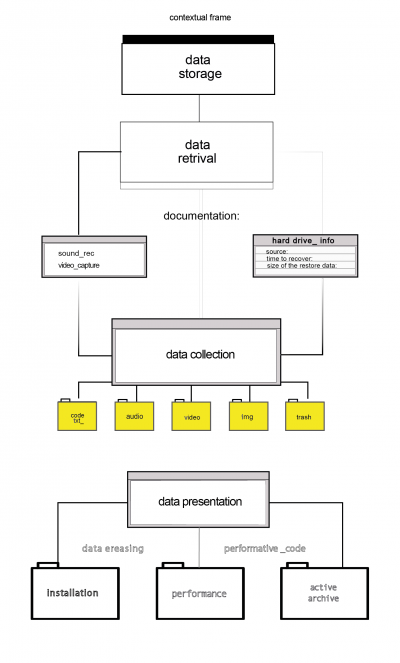
I built a simple methodology of data recovery. The data storage is the approached collection of ten hard drives followed by information about the hard drive: the source of origin()
The documentation or the process of recovery consists of video capture of the used software and sound from a spinning hard drive disk (unable to boot). In order to organize this accidentally found archive I simply described the size/ model of each hard drive, the process of the remain time and amount of the restored data.
Data collection consists of rich content of personal data: img files, videos files, audio files, code or text logs and trash (or unrecoverable files or parasite files etc.)
Sample of found material:
- The factory set is a 23 min long video documentation of factory for pineapples in Ghana.
The camera follows the production line of workers assembling pineapples, scene by scene revealing every detail of the process.
The moving images are rich by their source of origin, drawing highly graphical, dense scene of workers in factory motionless in their every day basics.
The images serve as a data trails, conveying the trace of the failure of the recovery process, signed for being "broken" or interrupted. Sometimes the freeze of the frame creates conscious break from the meditation, but also suggest that the footage has been manipulated.
PRACTICE – BASED
Descriptions of previous projects